Sudo (user permissions) is used on a Linux VPS (virtual private server) to secure your SSH access and reduce the risk of unauthorised intrusion. This guide explains how to create a new user, grant sudo rights, and disable direct root login on a Loopia VPS managed through the Customer Zone.
Create a new user
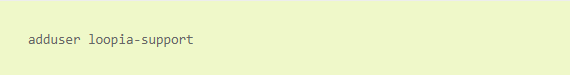
In the following example we use the username loopiasupport, but you can of course choose something else. Run the following command:
Please choose a personal username that is not associated with your organisation, and avoid common usernames such as admin, as these are frequent targets for intrusion attempts. When you run the command you will be asked to set a password and to fill in a few other fields. Only the password is required — the rest can be left blank.
Keep in mind that the username, like everything else in most Unix environments, is case sensitive: “Loopia Support” is not the same as “loopia support”.
Give the user temporary administrative rights
The user you just created has no rights to run administrative commands. Giving a user the ability to run any command at any time is a major security risk, so we will use sudo instead. Sudo gives the user temporary administrative rights only when needed.
To run a command with administrative privileges, simply type sudo before the command, for example sudo apt-get update.
Grant sudo rights with the following command:
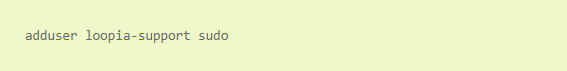
This adds the user loopiasupport to the sudo group. All users in the sudo group can run commands as administrator.
Alternative: use visudo
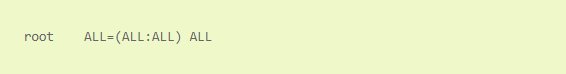
An alternative is the visudo command. Running visudo opens a text file that contains a line that looks like this:
Copy the entire line, paste it just below, and replace root with your username:
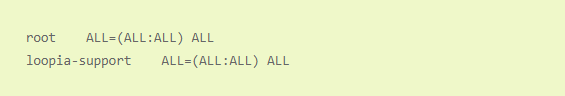
When you save the file, the user will be able to use sudo. To test this you can switch to the new user with the su loopiasupport command (replace loopiasupport with your chosen username). Because you are logged in as root when you run this command, you do not need to enter a password — you will be logged in directly as the new user.
Authenticate the user to run sudo
To run sudo, you must authenticate yourself by entering the user’s password. After you do, you remain authenticated for five minutes. During that period you still need to type sudo in front of each command, but you do not have to re-enter the password each time. This is often called “running a command as root”, even though the root username is not actually used — for simplicity we use that phrase throughout this guide.
If everything works properly, close the connection to your VPS and reconnect using your new username.
Turn off the ability to log in as root
As mentioned, over 98% of SSH intrusion attempts use the username root. A very simple way to protect against these is to disable the ability to log in as root.
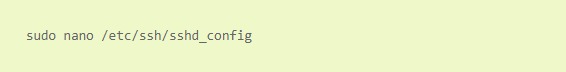
Edit the /etc/ssh/sshd_config file. If you followed our previous instructions you probably do not have an editor installed, so we recommend installing nano, a simple editor. Then open the file with the following command:
Find this line:
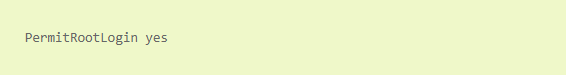
Change yes to no.
Optional: change the SSH port
By default, SSH uses port 22. To increase security further, you can change the Port 22 line to any port between 1 and 65535. Choose a fairly high number to reduce the risk of colliding with another service you may use later.
Save and restart SSH
Save the file and close it. In nano, press Ctrl + X. If you have made changes, the program will ask whether you want to save them; press Y and then Enter. For the new settings to take effect, restart the SSH server:
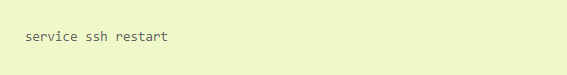
From now on, anyone trying to log in as root via SSH will receive a login-failed error, as if they had entered an incorrect password. If you changed the SSH port, remember to specify the new port whenever you connect to your server.
Tip: If you accidentally lock yourself out, you can still log in as root via the Screen Console available in your Loopia Customer Zone, because it does not connect via SSH.